Elastic Global Threat Report 2023 Reveals Dominance of Ransomware
18 Octobre 2023 - 12:00PM
Business Wire
Increases in ransomware, commercial
off-the-shelf malware, and attacks against cloud service providers
create new challenges for cybersecurity teams
Elastic® (NYSE: ESTC) ("Elastic"), the company behind
Elasticsearch®, today announced its second Elastic Global Threat
Report, issued by Elastic Security Labs. Based on observations from
more than 1 billion data points over the last 12 months, the report
reveals ransomware is expanding and diversifying; more than half of
all observed malware infections were on Linux systems; and
credential access techniques have become an essential part of the
cloud intrusion process.
Key findings from the report include:
Malware Trends
The majority of malware observed was composed of a small number
of highly prevalent ransomware families and commercial
off-the-shelf (COTS) tools. As financially motivated threat
communities adopt or offer malware-as-a-service (MaaS)
capabilities, enterprises should heavily invest in developing
security functions with broad visibility of low-level behaviors to
expose previously undiscovered threats.
- BlackCat, Conti, Hive, Sodinokibi and Stop are the most
prevalent ransomware families we identify through signatures,
amounting to about 81% of all ransomware activity.
- COTS malware capabilities like Metasploit and Cobalt Strike
represented 5.7% of all signature events. On Windows, these
families amounted to about 68% of all infection
attempts.
- Around 91% of malware signature events came from Linux
endpoints, while Windows endpoints accounted for only about
6%.
Endpoint Behavior Trends
The most sophisticated threat groups evade security by
withdrawing to edge devices, appliances, and other platforms where
visibility is at its lowest. As never before, the report highlights
the need for enterprises to evaluate the tamper-resistant nature of
their endpoint security sensors and consider monitoring projects to
track vulnerable device drivers used to disable security
technologies. In addition, organizations with large Windows
environments should track vulnerable device drivers to disable
these essential technologies.
- When looked at together, Execution and Defense Evasion make up
more than 70% of all endpoint alerts.
- Elastic observed the most discreet techniques on Windows
endpoints, being the top target by adversaries with 94% of
all endpoint behavior alerts, followed by macOS at 3%.
- macOS-specific credential dumping was responsible for an
astounding 79% of all credentials access techniques by
adversaries, an increase of approximately 9% since last
year. Of these attempts, we observed that Windows environments
where ProcessDump.exe, WriteMiniDump.exe, and RUNDLL32.exe were
used more than 78% of the time.
Cloud Security Trends
As enterprises increasingly migrate on-premises resources to
hybrid or entirely cloud-based environments, threat actors are
taking advantage of misconfigurations, lax access controls,
unsecured credentials, and no functional principle of least
privilege (PoLP) models. Organizations can dramatically reduce the
risk of compromise by implementing the security features that their
cloud providers already support and monitoring for common
credential abuse attempts.
- For Amazon Web Services, Elastic observed defense evasion
(38%), credential access (37%), and execution
(21%) as the most common tactics mapped to threat detection
signals.
- 53% of credential access events were tied to compromised
legitimate Microsoft Azure accounts.
- Microsoft 365 experienced a high rate of credential access
signals, accounting for 86%.
- 85% of Google Cloud threat detection signals were
related to defense evasion.
- Discovery accounted for approximately 61% of all
Kubernetes-specific signals, predominantly related to unexpected
service account requests that were denied.
“Today’s threat landscape is truly borderless, as adversaries
morph into criminal enterprises focused on monetizing their attack
strategies,” said Jake King, head of security intelligence and
director of engineering at Elastic. “Open source, commodity
malware, and the use of AI have lowered the barrier to entry for
attackers, but we’re also seeing the rise of automated detection
and response systems that enable all engineers to better defend
their infrastructures. It’s a cat-and-mouse game, and our strongest
weapons are vigilance and the continued investment in new defense
technologies and strategies.”
Additional Resources
Download the report Read the blog Join the webinar
About the Report
The 2023 Elastic Global Threat Report is a summary of
observations distilled down to a small number of distinct
categories. The report is based on Elastic telemetry, public, and
third-party data voluntarily submitted to surface threats based on
observations from more than 1 billion data points over the last 12
months. All information has been responsibly sanitized where
applicable to protect the identities of those involved.
About Elastic
Elastic (NYSE: ESTC) is a leading platform for search-powered
solutions. Elastic understands it's the answers, not just the data.
The Elasticsearch platform enables anyone to find the answers they
need in real-time using all their data, at scale. Elastic delivers
complete, cloud-based, AI-powered solutions for enterprise
security, observability and search built on the Elasticsearch
platform, the development platform used by thousands of companies,
including more than 50% of the Fortune 500. Learn more at
elastic.co
View source
version on businesswire.com: https://www.businesswire.com/news/home/20231018031597/en/
Candace Metoyer Elastic Public Relations PR-Team@elastic.co
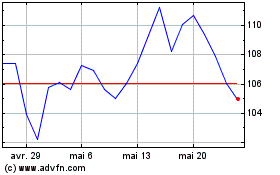
Elastic NV (NYSE:ESTC)
Graphique Historique de l'Action
De Avr 2024 à Mai 2024
Elastic NV (NYSE:ESTC)
Graphique Historique de l'Action
De Mai 2023 à Mai 2024
